The promise of “chat-to-build” AI is simple: describe your vision, and the platform handles the rest. But for users of Lovable, the Stockholm-based unicorn valued at over $6.6 billion, that magic just turned into a security nightmare. At the heart of the scandal is a Broken Object Level Authorization (BOLA) vulnerability, a common but devastating API flaw where a system verifies who a user is, but fails to check if they actually have permission to access a specific resource.
A massive disclosure has revealed that if you built a project on the platform before November 2025, this flaw meant your code, credentials, and private conversations have been sitting in the open, and the company’s defensive response is raising even more eyebrows.
The Vulnerability: A “Front Door” Without a Lock
In plain English: Lovable’s API checked if you were logged in, but it never checked if you actually owned the project you were looking at.
By simply changing a project ID in a URL, anyone with a free account could bypass security and pull down entire source trees. Security researcher @weezerOSINT, who blew the whistle on the flaw, demonstrated the severity by accessing an actively developed admin panel for a real-world non-profit. The data exposed wasn’t just “public” fluff—it included .env files, live Supabase URLs, and sensitive API keys.
The Confessional: Why AI Chat Logs Are a Goldmine
The most devastating part of this leak isn’t just the code; it’s the AI chat histories.
When developers use AI to build apps, they treat the chat box like a private workspace. They paste in error logs, discuss proprietary business logic, and share database schemas to help the AI debug. Because of this bug, those “private” conversations were readable by anyone.
-
PII Leakage: Chat logs revealed database structures containing
email,first_name, andstripe_customer_id. -
Hardcoded Secrets: Developers routinely dropped live credentials into the chat to get the AI to fix connection issues.
-
Global Enterprise Exposure: With 30,000 paying customers and users from tech giants like Nvidia, Microsoft, and Uber, the logs suggest that internal corporate workflows and innovation groups have been exposed.
Lovable Pushes Back: “Feature, Not a Bug?”
Following the public outcry, Lovable issued an official statement that essentially doubles down on their design choices while admitting to a massive communication failure.
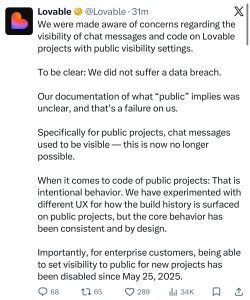
Their defense rests on three main points:
-
The “No Breach” Claim: Lovable insists this wasn’t a hack, but rather a result of projects being set to “public.”
-
The Documentation Fail: They admit it was “unclear” that making a project public would also expose every private AI chat message used to build it. They have since disabled chat visibility for public projects.
-
Intentional Code Exposure: They maintain that for public projects, the visibility of the source code is a core feature of the platform’s UX.
The 48-Day Silence
Despite the “it’s a feature” defense, the timeline tells a different story. The vulnerability was reported to Lovable via HackerOne on March 3, 2026.
Instead of a platform-wide fix, Lovable quietly patched the API for new projects, which began returning a 403 Forbidden error. However, they left every legacy project—the ones with months of sensitive data—wide open. It took 48 days and a public “full disclosure” on Twitter for the company to address the exposure for their oldest, most loyal users.
Editor’s Note
This incident is a massive red flag for the entire AI-assisted development ecosystem. As “vibe-coding” becomes the standard for rapid prototyping, the rush to ship “magic” tools is leading to the abandonment of Day-1 security fundamentals.
If you are one of the hundreds of thousands of users on Lovable:
-
Assume you are compromised: If your project was created before November 2025, treat your data as leaked.
-
Rotate Everything: Change your Supabase keys, database passwords, and API tokens immediately.
-
Sanitize Your Prompts: Never paste a live secret into an AI chat. Treat the prompt box as a public forum, because as Lovable just proved, security is often treated as a secondary feature to “vibes.”